Application firewall Douane for ArchLinux
While reading the Wikileaks publications about the internal CIA malware production, I became aware that these engineers had to cope with several security products on the MacOS X platform, to safely install their monitoring software and to avoid being detected by third-party firewalls. One document published, describes how the remote-control software “DerStarke” is able to hide its traffic by inheriting into an unsuspicious process like Safari. They further note, that this method successfully circumvents application firewalls like “Little Snitch“.
These insights into govermental intelligence operations show that even products considered to be more secure, like MacOS X, are still vulnerable to these kind of attacks. But on the the contrary, security messures like application sandboxing and firewalling, makes it more complicated for intruders to bypass everything without being recognized.
I was then looking into an application firewall solution for Linux systems and found out about Douaneapp. Even though the software looked a bit unstable and discontinued, I gave it a try.
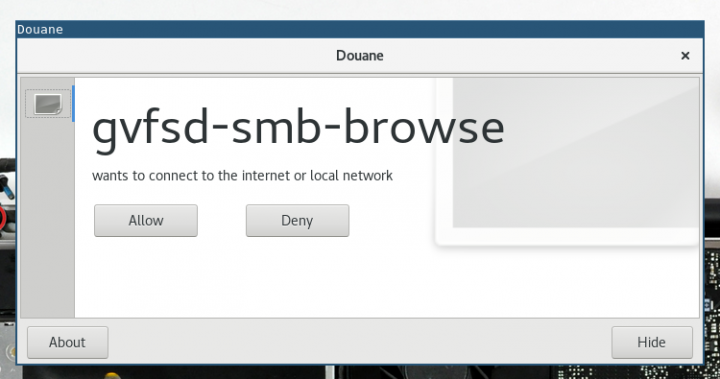
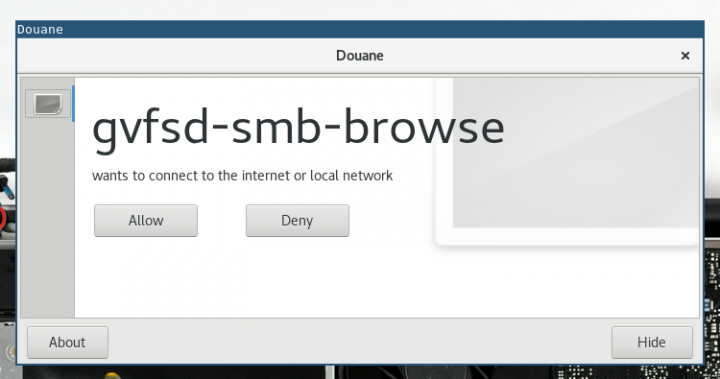
Douane is a bit difficult to install but I was able to get it working. The program consists of a kernel module, which is able to block outgoing connections per process, a daemon and a dialog process. After installing and running everything, a small popup window appears, asking for permissions.
I enhanced the ArchLinux packages and applied some patches to the software, so it is now easier to get started:
pacaur -S douane-dkms-git douane-daemon-git douane-dialog-gitAfter installation, start the daemon:
sudo systemctl daemon-reload
sudo systemctl start douane-daemonEnsure that the dialog process is started with your desktop:
/opt/douane/bin/douane-dialogThats it! In case the daemon won’t start, it could be that you have to manually load the kernel module:
sudo modprobe douane
lsmod | grep douaneI really hope that the development of this application continues. If you know any alternatives to this app, please let me know and drop a comment :)
There’s an open source version of LittleSnitch for Linux:
https://github.com/evilsocket/opensnitch
And SubgraphOS seems to have an application firewall of some kind:
https://github.com/subgraph/fw-daemon
Douane is superior to OpenSnitch. Douane is all we need from a per application firewall.